密码学第二次实验,主要是块密码和应用实例。
任务一
填充提示攻击(padding oracle attack)
攻击条件:
- 攻击者能够获取到密文(基于分组密码模式),以及IV向量(通常附带在密文前面);
- 攻击者能够修改密文触发解密过程,解密成功和解密失败存在差异性。
解题思路
构造IV全0,从中间值的最后一个字节开始爆破,IV的最后一个字节遍历0x01~0xFF,若提示解密成功,根据PKCS#5填充规则,可逆推出中间变量。更新IV,从后向前猜解中间值,最后将得到的中间值和正确的IV异或,即可得到明文。
代码
from oracle import *
import re
C = ['9F0B13944841A832B2421B9EAF6D9836', '813EC9D944A5C8347A7CA69AA34D8DC0', 'DF70E343C4000A2AE35874CE75E64C31']
Oracle_Connect()
Message = []
Iintermediary_VALUE = []
for b in range(2): # 对2组中间值的爆破是相同的
Ture_IV = C[b]
Iintermediary_value = []
Fake_IV = ['00', '00', '00', '00', '00', '00', '00', '00', '00', '00', '00', '00', '00', '00', '00', '00']
# 初始化Fake_IV
padding = 1
for i in range(15, -1, -1): # 从中间值的最后一个字节开始爆破
for j in range(15, i, -1):
Fake_IV[j] = hex(int(Iintermediary_value[15 - j], 16) ^ padding)[2:].zfill(2) # 构造IV,使后面字节均满足当前填充条件
for n in range(256): # 每次爆破一个字节,遍历0x00-0xFF
Fake_IV[i] = hex(n)[2:].zfill(2)
data = ''.join(Fake_IV) + C[b + 1] # 拼接构造的IV和正确密文
ctext = [(int(data[i:i + 2], 16)) for i in range(0, len(data), 2)]
rc = Oracle_Send(ctext, 2)
if str(rc) == '1': # Padding正确时, 记录Ivalue, 结束爆破
Iintermediary_value += [hex(n ^ padding)[2:].zfill(2)] # 逆序存储
# print(hex(n ^ padding)[2:].zfill(2))
break
padding += 1
Iintermediary_value = ''.join(Iintermediary_value[::-1])
Iintermediary_VALUE += [Iintermediary_VALUE]
# Ture_IV与中间值异或可以直接得到密文对应的明文,而无需密钥
m = re.findall('[0-9a-f]+', str(hex(int(Ture_IV, 16) ^ int(Iintermediary_value, 16))))[1].decode('hex')
Message += [m]
Oracle_Disconnect()
print('The Iintermediary_VALUE is:', ''.join(Iintermediary_VALUE))
print('The Message is:', ''.join(Message))
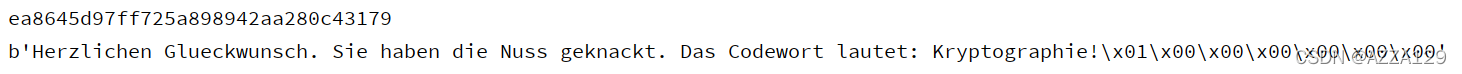
运行结果

任务二
题目链接:Set 2 - The Cryptopals Crypto Challenges
Byte-at-a-time ECB decryption
AES-128-ECB(random-prefix || attacker-controlled || target-bytes, random-key)
参考文章
解题思路
求target-bytes的长度和加密块的大小。
(1)通过不断对"A"、"AA"、"AAA"……加密,通过密文块的长度以及填充规则,可以得到random-prefix + target-bytes的总长度以及加密块的大小。
(2)加密两个块大小的"A"列表,然后不断的添加"A",当出现两个相同的块的时候,可以得到单独random-prefix的填充长度。
(3)加密三个块大小的"A",找到其中的两个相同块,则第一个相同块前面部分为random-prefix及其填充,从而可以得到random-prefix的长度;从总长度中减掉random-prefix长度,即为target-bytes的长度。
代码
import os
import base64
import random
from Crypto.Cipher import AES
from AES_CBC import *
b64_string = "Um9sbGluJyBpbiBteSA1LjAKV2l0aCBteSByYWctdG9wIGRvd24gc28gbXkgaGFpciBjYW4gYmxvdwpUaGUgZ2lybGllcyBvbiBzdGFuZGJ5IHdhdmluZyBqdXN0IHRvIHNheSBoaQpEaWQgeW91IHN0b3A/IE5vLCBJIGp1c3QgZHJvdmUgYnkK"
random_key = os.urandom(16)
random_string = os.urandom(random.randint(0, 255))
def AES128_harder(text: bytes) -> bytes:
global b64_string, random_key, random_string
secret_string = base64.b64decode(b64_string)
plaintext = random_string + text + secret_string # 随机前缀 + 攻击者控制 + 目标字节
cipher = AES_ECB_encrypt(plaintext, random_key)
return cipher
def break_AES_ECB_harder(keysize: int, encryptor: callable) -> bytes:
# 寻找前缀长度
padding = 0
random_blocks = 0
cipher_length = len(encryptor(b''))
prefix_length = len(os.path.commonprefix([encryptor(b'AAAA'), encryptor(b'')]))
print("Prefix length: ", prefix_length)
# 查找随机块的数量
for i in range(int(cipher_length / keysize)):
if prefix_length < i * keysize:
random_blocks = i
break
print("Random blocks: ", random_blocks)
# 查找所需的字节填充数
base_cipher = encryptor(b'')
for i in range(1, keysize):
new_cipher = encryptor(b'A' * i)
new_prefix_length = len(os.path.commonprefix([base_cipher, new_cipher]))
if new_prefix_length > prefix_length:
padding = i - 1
break
base_cipher = new_cipher
print("Number of bytes of padding required: ", padding)
deciphered = b""
ciphertext = encryptor(deciphered)
# 添加了填充,增加了一个块
run = len(ciphertext) + keysize
for i in range(keysize * random_blocks + 1, run + 1):
template = b'A' * (run - i + padding)
cipher = encryptor(template)
for j in range(256):
# print(i, j)
text = template + deciphered + j.to_bytes(1, "little")
c = encryptor(text)
if c[run - keysize:run] == cipher[run - keysize:run]:
deciphered += chr(j).encode()
break
return PKCS7_unpad(deciphered)
keysize = 16
byte_text = break_AES_ECB_harder(keysize, AES128_harder)
print("\nDeciphered string:\n")
print(byte_text.decode("utf-8").strip())
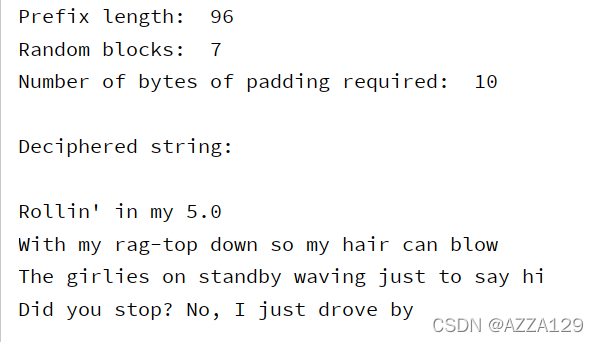
运行结果
PKCS#7 padding validation
在之前实现的CBC模式基础上,实现PKCS#7填充验证。
代码
from AES_CBC import *
given_string = "ICE ICE BABY\x04\x04\x04\x04"
target_string = "ICE ICE BABY"
try:
target_string.encode() == PKCS7_unpad(given_string.encode())
print("Correct Padding!")
except:
print("Incorrect Padding!")
运行结果
Correct Padding!
CBC比特翻转攻击(CBC bitflipping attacks)
参考文章
CBC Bitflipping Attacks | full-stack overflowEven though CBC is more secure than ECB, it is still vulnerable to attacks without taking additional precautions like using a Message Authentication Code (MAC). Cryptopals Set 2 Challenge 16.![]() https://thmsdnnr.com/blog/cbc-bitflipping-attacks/CBC的比特翻转攻击,通过添加很长的data构造出一个没有意义的块,然后异或这个块的某个密文字节,这样下一块的明文字节在解密时就会被篡改。
https://thmsdnnr.com/blog/cbc-bitflipping-attacks/CBC的比特翻转攻击,通过添加很长的data构造出一个没有意义的块,然后异或这个块的某个密文字节,这样下一块的明文字节在解密时就会被篡改。
代码
import os
import random
from Crypto.Cipher import AES
from AES_CBC import *
prepend_string = "comment1=cooking%20MCs;userdata="
append_string = ";comment2=%20like%20a%20pound%20of%20bacon"
parameter = b";admin=true;"
keysize = 16
random_key = os.urandom(keysize)
IV = os.urandom(keysize)
def encryptor(text: bytes, IV: bytes, key: bytes) -> bytes:
# 将给定的字符串添加到自定义文本中,并通过AES_CBC模式进行加密
plaintext = (prepend_string.encode() + text + append_string.encode()).replace(b';', b'";"').replace(b'=', b'"="')
ciphertext = AES_CBC_encrypt(PKCS7_pad(plaintext, len(key)), IV, key)
return ciphertext
def decryptor(byte_string: bytes, IV: bytes, key: bytes) -> bool:
# 通过AES_CBC模式解密给定的密文并检查admin是否设置为true
decrypted_string = PKCS7_unpad(AES_CBC_decrypt(byte_string, IV, key))
if b";admin=true;" in decrypted_string:
return True
else:
return False
def CBC_bit_flipping(parameter: bytes, keysize: int, encryptor: callable) -> bytes:
# 填充
padding = 0
random_blocks = 0 # 寻找前缀长度
cipher_length = len(encryptor(b'', IV, random_key))
prefix_length = len(os.path.commonprefix([encryptor(b'AAAA', IV, random_key), encryptor(b'', IV, random_key)]))
print("Prefix length: ", prefix_length)
# 查找随机块的数量
for i in range(int(cipher_length / keysize)):
if prefix_length < i * keysize:
random_blocks = i
break
print("Random blocks: ", random_blocks)
# 查找所需的字节填充数
base_cipher = encryptor(b'', IV, random_key)
for i in range(1, keysize):
new_cipher = encryptor(b'A' * i, IV, random_key)
new_prefix_length = len(os.path.commonprefix([base_cipher, new_cipher]))
if new_prefix_length > prefix_length:
padding = i - 1
break
base_cipher = new_cipher
print("Number of bytes of padding required: ", padding)
# 翻转给定字符串的字节
input_text = b'A' * padding + b"heytheremama"
string = parameter
modified_string = b""
ciphertext = encryptor(input_text, IV, random_key)
for i in range(len(string)):
modified_string += (ciphertext[i + (random_blocks - 1) * keysize] ^ (input_text[i + padding] ^ string[i])).to_bytes(1, "big")
modified_ciphertext = ciphertext[:(random_blocks - 1) * keysize] + modified_string + ciphertext[(random_blocks - 1) * keysize + len(modified_string):]
return modified_ciphertext
modified_ciphertext = CBC_bit_flipping(parameter, keysize, encryptor)
print(AES_CBC_decrypt(modified_ciphertext, IV, random_key))
运行结果
Prefix length: 32
Random blocks: 3
Number of bytes of padding required: 10
b'comment1"="cooking%20MCs";"userd\xc3\x9c\xc3\xaf\x13\xc2\xa0\x10k\xc3\x90\xc2\x94(Q\x14S\xc2\xb4z\xc3\xb2\xc2\x85;admin=true;";"comment2"="%20like%20a%20pound%20of%20bacon\x06\x06\x06\x06\x06\x06'
任务三
MTC3 AES key — encoded in the machine readable zone of a European ePassport
一个密码应用实例,思路很好理解,主要考察对密码组件的应用,较难的地方在于对文档的理解。
代码
from hashlib import sha1
import codecs
import base64
from Crypto.Cipher import AES
import binascii
"""求未知数,是到期日的校验位,根据校验规则计算"""
def Unknown_Number() -> int:
Unknown_Number = 0
number = "111116"
weight = "731"
for i in range(0, len(number)):
Unknown_Number += int(number[i]) * int(weight[i % 3])
return Unknown_Number % 10
"""计算k_seed"""
def cal_Kseed() -> str:
MRZ_information = "12345678<811101821111167"
# 护照号码+校验位+出生日期+校验位+到期日+校验位(包括"<"符号)
H_information = sha1(MRZ_information.encode()).hexdigest()
# 十六进制字符串
K_seed = H_information[0:32]
# 最高有效16字节用作K_seed
return K_seed
def cal_Ka_Kb(K_seed):
c = "00000001"
d = K_seed + c
H_d = sha1(codecs.decode(d, "hex")).hexdigest()
# 十六进制先变为二进制散列再转换成十六进制
ka = H_d[0:16]
kb = H_d[16:32]
return ka, kb
"""对Ka和Kb分别进行奇偶校验,得到新的k1和k2"""
def Parity_Check(x):
k_list = []
a = bin(int(x, 16))[2:]
# 16进制字符串转2进制字符串
for i in range(0, len(a), 8):
# 7位一组分块,计算一个校验位,使1的个数为偶数
# 舍弃原来的第8位
if (a[i:i + 7].count("1")) % 2 == 0:
k_list.append(a[i:i + 7])
k_list.append('1')
else:
k_list.append(a[i:i + 7])
k_list.append('0')
k = hex(int(''.join(k_list), 2))
return k
if __name__ == "__main__":
K_seed = cal_Kseed()
ka, kb = cal_Ka_Kb(K_seed)
# print(ka, kb)
k_1 = Parity_Check(ka)
k_2 = Parity_Check(kb)
# print(k_1, k_2)
key = k_1[2:] + k_2[2:]
print(key)
ciphertext = base64.b64decode(
"9MgYwmuPrjiecPMx61O6zIuy3MtIXQQ0E59T3xB6u0Gyf1gYs2i3K9Jxaa0zj4gTMazJuApwd6+jdyeI5iGHvhQyDHGVlAuYTgJrbFDrfB22Fpil2NfNnWFBTXyf7SDI")
IV = '0' * 32
m = AES.new(binascii.unhexlify(key), AES.MODE_CBC, binascii.unhexlify(IV)).decrypt(ciphertext)
print(m)
运行结果